Deception is used in several conflicts to strategically manipulate adversary beliefs, goals, and actions. Cyber deception, such as deploying honeypots, can slow the attacker, waste his time, and detect their intention. Thus, cyber deception has become a crucial strategy for misleading attackers and protecting critical assets in the digital realm. Similarly, physical deception tactics like using decoys and misinformation are used to safeguard valuable resources. Consider a multi-domain cyber psychical system where elements of the physical domain are connected to the elements of the cyber domain and security in one domain affects the other. In such scenarios, when cyber and physical security strategies are designed independently, they often lack coordination, creating vulnerabilities that adversaries can exploit across both domains.
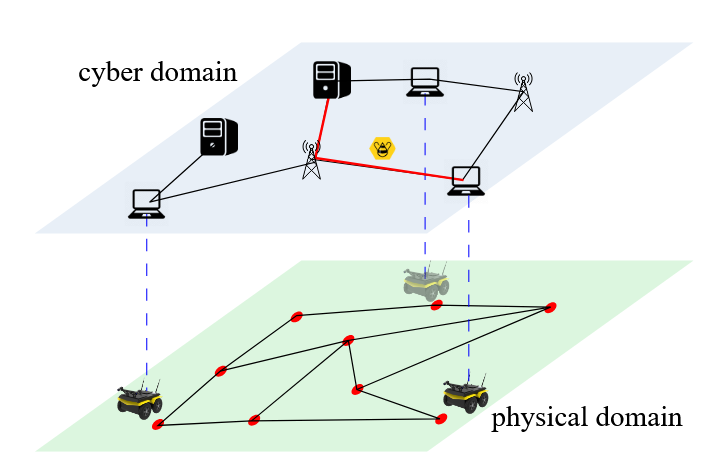
Cyber-Physical Systems are critical infrastructure components that integrate computational and physical processes, particularly vital in industries like water treatment. However, their growing interconnectivity has exposed them to sophisticated Multi-Domain Advanced Persistent Threats that simultaneously exploit network vulnerabilities and manipulate physical components. Recent incidents demonstrate the severity of this threat landscape. These real-world attacks underscore the inadequacy of traditional single-domain security approaches. Game theoretic frameworks are useful to model these multi-domain deception scenarios since it includes adversarial players. Deep Reinforcement learning algorithms are increasingly employed to analyze patterns in large datasets, enabling the prediction of adversary behavior and the real-time adaptation of deception strategies. Another promising research direction for deception involves using Intent-Based Networking (IBN) frameworks for automated deception orchestration. The objectives of this project are to build a multi domain deception framework that creates coherent fake scenarios across network and physical domains, ensure deception strategies remain believable and consistent over time, counter any actions attackers might use to detect or circumvent the deception, maintain long-term multi-domain deception consistency through coordinated cyber and physical strategies, and deploy adaptive decoys in real-time to mislead attackers without causing real system damage.