Members
Permanent members
- David Beserra (Associate professor, Paris)
- Nidà Meddouri (Associate professor, Paris)
- Pierre Parrend (Full professor, Strasbourg)
Postdocs
- Abdel-Qadir Khan (Paris)
PhD Students
- Bertrand Tsagué (Paris, with University of NGaoundere and US DEVCOM Army Research Laboratory)
- Juliette Jacquot (Rennes, with IRISA, since 2025)
- Maya Mouhamad (Paris, CIFRE with APL Datacenter)
- Côme Frappé--Viallatoux (Strasbourg, ANR Correau Project with Unistra)
- Julien Michel (Strasbourg, projet AID RAPID Damiage)
Former members
- Majed Jaber, PhD on Analyse structurelle et spectrale des graphes dynamiques pour la détection des attaques, defense on 19/12/2026
- Amani Abou Rida, PhD on Enhancing detection and explainability in cybersecurity : a shift from machine learning to graph learning, defense on 24/01/2024
Research
Keywords
- Evaluation, Feature analysis, Graphs, Learning Gen AI, Data management, Systems, High Performance Computing
Context and Motivation
Anomalies in computer networks, Operating Systems, or distributed critical applications are extremely costly and hinder digital development.
The SECUSYS Team proposes novel statistics, machine learning and generative AI models to study impact of technical mechanisms and data structures on the security, stability and performance of these systems.
Research Objectives
The detection and characterization of emergent behaviours in complex systems build the core research challenge od the 'Detection & Evaluation' thematics: how to define methodologies and best practices for identifying nominal as well as anomalous behaviours in systems ? What is the impact of distributed mechanisms on these methodologies ? These are the question that we study.
Societal security challenges like the rise in cybercrime and terrorist acts is also considered in our research projects.
Main Research Axes
The challenges we address are:
- For learning
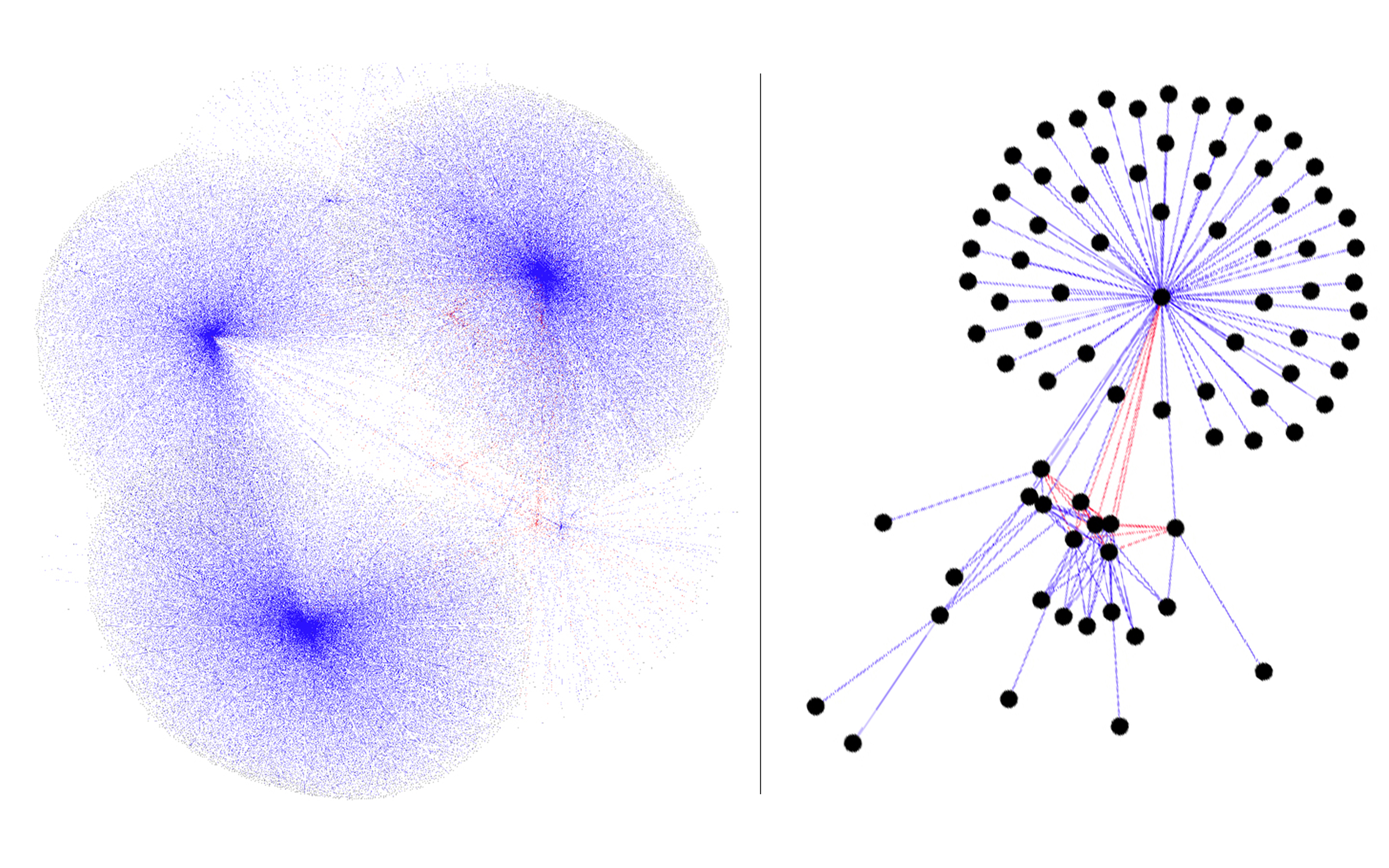
- Contribution of topological analysis to attack detection: statistical distributions, community and spectral graphs models
- Characterization and detection of concept drift
- Detection of anomalies in critical cyberphysical systems (CPS) and IoT: medical, water distribution
- For evaluation
- Impact of low level systems (ARM, RISC V) to performance reliability and security
- Impact of virtualization technologies on system performance
Application domains
- Virtualization
- Critical System: ICS & IoT, Software defined vehicles
- Defensive security, Offensive security
- Physical security
Software
- GPML: a library for extracting graph-based features from traffic traces for extracting security-relevant behavior
- RedTeamLLM: an agentic framework for offensive security
Some Projects
Collaborative Projects
- GAML-MUDIT, with University of NGaoundere and US DEVCOM Army Research Laboratory
We also contribute to following projects:
- ANR Correau (with ICube / University of Strasbourg)
Industrial Projects
- CIFRE with APL Datacenter, on Prédiction des intrusions réseau par apprentissage fédéré et interprétable des anomalies dans un environnement distribué
Ongoing Student Projects
- Agentic AI for offensive security: Architecture, optimization and Security Model (Parcours recherche EPITA)
- Federated Anomaly Network Learning over Distributed Data Streams (Parcours recherche EPITA)
- Evaluation of virtualized infrastructure performances for High Performance Computing (Parcours recherche EPITA)
- Anomaly detection in encrypted traffic (Parcours recherche EPITA)
Related Projects
DAMIAGE
DGA Rapid DAMIAGE project, "Detection of Attacks and Threats for Large-Scale Infrastructures".
GAML-MUDIT
Cyber-Physical Systems (CPS), such as those used in water treatment, are increasingly exposed to sophisticated multi-domain Advanced Persistent Threats that exploit both network vulnerabilities and physical processes, revealing the limits of traditional single-domain security. This project proposes a multi-domain deception framework that combines game theory, deep reinforcement learning, and intent-based networking to orchestrate adaptive, believable cyber-physical decoys that mislead attackers and maintain consistent long-term deception without harming real systems.
Software Defined Vehicle Security
The goal of this project is the design of an approach to secure CAV nodes and the end-to-end interactions between the TCU and the V2X application services. To this end, we rely on bio-inspired techniques.
XDGMed
Explainable attack Detection using Graphs for Medical devices.
Related Publications
[1]
Frappé-Vialatoux, Côme • Parrend, Pierre. "Introducing H-Leading-Ones as a Mixed-Category Benchmark Problem for Evolutionary Algorithms". Genetic and Evolutionary Computation Conference (GECCO). 2025. https://doi.org/10.1145/3712255.373426.
[2]
Jaber, Majed • Parrend, Pierre • Boutry, Nicolas. "Spectral Graph Analysis of Bipartite Graphs for Advanced Attack Detection". European Interdisciplinary Cybersecurity Conference (EICC25). 2025. https://doi.org/10.1007/978-3-031-94855-8_16.
[3]
David Beserra • Robert Nantchouang • Mickael Chau and Patricia Takako Endo • Jean Araujo • Marc Espie. "How Effective are OS-level Virtualization Tools for Managing Containers?". 39th International Conference on Advanced Information Networking and Applications (AINA-2025). 2025. https://doi.org/10.1007/978-3-031-87772-8_13.
[4]
David Beserra • Jean Araujo. "An Enhanced Formalism for Resource Management Policies Specification and Fast Evaluation in Pervasive Systems". 39th International Conference on Advanced Information Networking and Applications (AINA-2025). 2025. https://doi.org/10.1007/978-3-031-87766-7_4.
[5]
Hermyson Oliveira • Kédna Camboim • David Beserra • Jean Araujo. "Performance Evaluation of IoT-Enabled Edge Computing Infrastructure for mHealth Services". 39th International Conference on Advanced Information Networking and Applications (AINA-2025). 2025. https://doi.org/10.1007/978-3-031-87766-7_27.
[6]
Antonio Carlos Sousa • David Beserra • Jean Araujo. "Performance Evaluation of Serverless Computing Infrastructure: Insights from Open-Source Frameworks". 39th International Conference on Advanced Information Networking and Applications (AINA-2025). 2025. https://doi.org/10.1007/978-3-031-87772-8_14.
[7]
Julien Michel • Pierre Parrend. "Graph-Based Intelligent Cyber Threat Detection System". Handbook of AI-Driven Threat Detection and Prevention: A Holistic Approach to Security. 2025.
[8]
David Beserra • Patricia Takako Endo • Louis Clinckx and Thomas Clement • Boubacar Guisse • Alexandre Maugras. "Raspberry Pi Single-Board Computers: Cost/Performance Rela onship Over Time". IEEE International Conference on Systems, Man, and Cybernetics. 2024. https://doi.org/10.1109/SMC54092.2024.10832006.
[9]
Côme Frappé-Vialatoux • Pierre Parrend. "Introducing Multi-Layer Concatenation as a Scheme to Combine Information in Water Distribution Cyber-Physical Systems". 28th International Conference on Knowledge-Based and Intelligent Information and Engineering Systems. 2024. https://doi.org/10.1016/j.procs.2024.09.690.
[10]
Côme Frappé-Vialatoux • Pierre Parrend. "Combining Physical and Network Data for Attack Detection in Water Distribution Networks". Water Distribution Systems Analysis (WDSA)/Computing and Control Water Industry (CCWI) Joint Conference. 2024. https://doi.org/10.3390/engproc2024069118.
[11]
Majed Jaber • Nicolas Boutry • Pierre Parrend. "Graph-Based Spectral Analysis for Detecting Cyber Attacks". ARES 2024 (The International Conference on Availability, Reliability and Security). 2024. https://doi.org/10.1145/3664476.3664498.
[12]
Hammi, Badis • Billot, Tristan • Bazain, Danyil and Binand, Nicolas • Jaen, Maxime • Mitta, Chems • El Madhoun, Nour. "An End-to-End Approach for the Detection of Phishing Attacks". Advanced Information Networking and Applications (AINA)). 2024. https://doi.org/10.1007/978-3-031-57916-5_27.
[13]
Meddouri, Nida • Leborgne, Aurélie • Salmon, Loic. "Actes de l'atelier Gestion et Analyse des données Spatiales et Temporelles". 2024.
[14]
Abou Rida, Amani • Amhaz, Rabih • Parrend, Pierre. "Metrics for Evaluating Interface Explainability Models for Cyberattack Detection in IoT Data". Complex Computational Ecosystems 2023 (CCE'23). 2023. https://doi.org/10.1007/978-3-031-44355-8_13.
[15]
Nida Meddouri • David Beserra. "Apprentissage interprétable de la criminalité en France (2012-2021)". Actes de l'atelier Gestion et Analyse des données Spatiales et Temporelles. 2024.
[16]
Melo, Pedro • Gama, Lucas • Dantas, Jamilson and Beserra, David • Araujo, Jean. "Performance Evaluation of Container Management Tasks in OS-Level Virtualization Platforms". 31th IEEE International Conference on Enabling Technologies: Infrastructure for Collaborative Enterprises (WETICE). 2023. https://doi.org/10.1109/WETICE57085.2023.10477783.
[17]
David Beserra • Nida Meddouri • Célia Restes • Anys Nait Zerrad and Basma Bouharicha • Aurore Duvernoy. "On the historical evolution of the performance versus cost ratio of Raspberry Pi computers". Conférence francophone d'informatique en Parallélisme, Architecture et Système (Compas 2023). 2023.
[18]
David Beserra • Marc Espie • Jean Araujo • Léo Tomasimo • Hector de Poncins • Hadrien-Samrek Lacombe • Thomas Vondracek. "Could the Topology of Virtual Processors Affect the Performance of a BSD-family OS Running in a VM?". 18th Iberian Conference on Information Systems and Technologies (CISTI'2023). 2023. https://doi.org/10.23919/CISTI58278.2023.10211928.
[19]
Ris, Simone • Araujo, Jean • Beserra, David. "A Systemic Mapping of Methods and Tools for Performance Analysis of Data Streaming with Containerized Microservices Architecture". 18th Iberian Conference on Information Systems and Technologies (CISTI'2023). 2023. https://doi.org/10.23919/CISTI58278.2023.10211834.
[20]
Meddouri, Nida • Leborgne, Aurélie • Salmon, Loic. "Actes de l'atelier Gestion et Analyse des données Spatiales et Temporelles". 2023.
[21]
Tristan Bilot • Grégoire Geis • Badis Hammi. "PhishGNN: A Phishing Website Detection Framework using Graph Neural Networks". Proceedings of the 19th International Conference on Security and Cryptography - SECRYPT. 2022. https://doi.org/10.5220/0011328600003283.
[22]
Abou Rida, Amani • Amhaz, Rabih • Parrend, Pierre. "Anomaly Detection on Static and Dynamic Graphs using Graph Convolutional Neural Networks". Robotics and AI for Cybersecurity and Critical Infrastructure in Smart Cities. 2022. https://doi.org/10.1007/978-3-030-96737-6_12.
[23]
Burger, Pauline • Colin, Florent • Coutelle, Romain • Strehle, Axelle • Mazzucotelli, Timothée • Collot, Nicole • Durand, Benjamin • Bouman, Arianne • Landau Prat, Daphna • Kleefstra, Tjitske • Parrend, Pierre • Piton, Amélie • Koolen, David and Mandel, Jean-Louis. "GenIDA: An International Participatory Database to Gain Knowledge on Health Issues Related to Genetic Forms of Neurodevelopmental Disorders". Journal of Neural Transmission. 2022. https://doi.org/10.1007/s00702-022-02569-3.